Securing DevOps environments is essential for protecting organizations against the growing threat of cyber attacks. By following the best practices, organizations can mitigate risks, reduce vulnerabilities, and build a strong security posture.
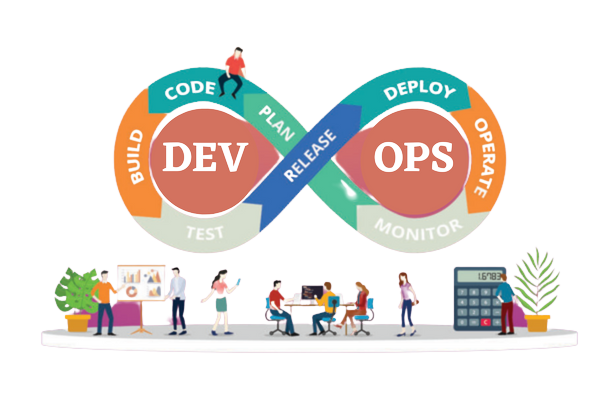
DevOps has revolutionized software development, enabling teams to build and deploy software faster than ever before. However, this new speed can come at a cost: security risks. The speed of DevOps means that security is often left behind, leading to vulnerabilities that can be exploited by attackers. Securing DevOps environments is crucial to mitigate the risks associated with deploying software quickly.
The Need for Securing DevOps Environments
The traditional model of software development involved separate teams responsible for coding, testing, and deploying software. However, DevOps combines these roles, allowing teams to deploy code multiple times per day. While this approach leads to faster software delivery, it also increases the risk of security breaches. DevOps environments are attractive targets for attackers because of the access they provide to sensitive data and resources.

Common Threats to DevOps Environments
There are several common threats to DevOps environments, including:
- Misconfigured cloud infrastructure
- Insecure coding practices
- Lack of security testing
- Insufficient access controls
- Phishing attacks
These threats can result in data breaches, denial-of-service attacks, and other types of cyberattacks. Organizations must take proactive steps to secure their DevOps environments to prevent these types of attacks.
Best Practices for Securing DevOps Environments
To secure DevOps environments, organizations must implement a comprehensive security strategy that covers every aspect of their software development lifecycle. Here are some best practices for securing DevOps environments:
-
Establish a Security-Focused Culture
Securing DevOps environments requires a cultural shift towards security. Everyone involved in the software development process, from developers to executives, must understand the importance of security and their role in maintaining it. Security should be a key part of the company culture, and security policies and procedures should be regularly reviewed and updated.
-
Limit Access to Sensitive Data and Resources
To limit the risk of data breaches, access to sensitive data and resources should be limited to only those who need them. Role-based access control (RBAC) can be used to restrict access to sensitive resources to only those who require it to perform their job duties.
-
Implement Role-Based Access Control
RBAC is a security model that restricts access to resources based on the roles of users within an organization. RBAC is an effective way to control access to resources in DevOps environments, as it limits the risk of unauthorized access to sensitive data and resources.
-
Automate Security and Compliance Checks
Automating security and compliance checks can help organizations identify and address security issues before they become a problem. Automated tools can scan code for vulnerabilities, check configurations for compliance with security policies, and monitor cloud infrastructure for security risks.
-
Use Security-Focused DevOps Tools
DevOps teams should use security-focused tools to ensure the security of their applications. Tools such as Snyk, Twistlock, and Aqua Security can help teams identify and fix vulnerabilities in their code and infrastructure.
-
Monitor for Anomalies and Respond Quickly
Organizations should monitor their DevOps environments for anomalies that could indicate a security breach. By using automated tools and implementing real-time monitoring, teams can quickly detect unusual activities or vulnerabilities, and address them before they can be exploited. Additionally, by regularly reviewing access controls and user permissions, organizations can prevent unauthorized access and ensure that only the necessary personnel have access to sensitive systems and data.
In addition to monitoring, incident response plans should be developed and tested to ensure that the organization can respond quickly and effectively to security incidents. The response plan should include a clear chain of command, defined roles and responsibilities, and procedures for communicating with stakeholders, including customers and partners. The plan should also be regularly reviewed and updated to address changes in the threat landscape and to ensure that it remains effective.
Finally, a culture of security should foster within the organization. All employees should train in basic security practices and should make aware of the potential risks associated with their activities. By encouraging shared responsibility for security, organizations can reduce the likelihood of a security breach and ensure that all team members are working towards the same goal.
Conclusion
Securing DevOps environments is essential for protecting organizations against the growing threat of cyber attacks. By following the best practices outlined above, organizations can mitigate risks, reduce vulnerabilities, and build a strong security posture. With the right approach, organizations can balance the need for speed and agility with the need for security. And drive innovation and growth in an ever-changing digital landscape.
BACK