The Internet of Things (IoT) has revolutionized the way we live and work, connecting devices and appliances to the internet to enable communication and automation.
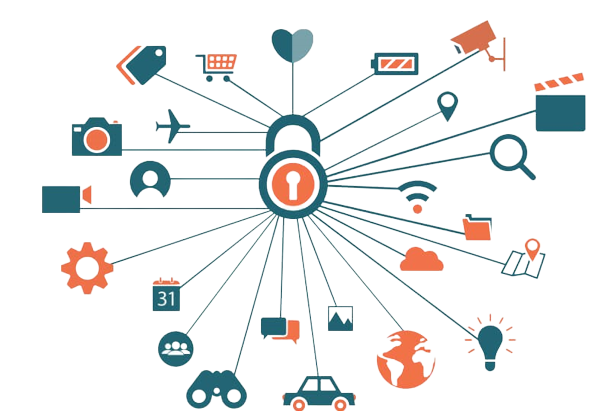
The Internet of Things (IoT) has revolutionized the way we live and work, connecting devices and appliances to the internet to enable communication and automation. While IoT devices bring immense benefits, they also pose significant security risks. From data breaches to device hijacking, the security of IoT devices must be taken seriously to protect both the device and the sensitive information it collects and stores. In this blog post, we will explore the best practices for building secure IoT devices, including securing data, networks, and devices.

Secure Data
One of the most critical aspects of securing IoT devices is protecting the data they collect and store. IoT devices collect vast amounts of data, including personal information, sensitive information, and more. To secure this data, it is essential to follow best practices, such as:
-
Encrypting Data in Transit and at Rest:
Encryption ensures that data has protected from unauthorized access, even if it is intercepted or accessed. Encrypting data both in transit (when it is transmitted from one device to another) and at rest (when it is stored on the device) helps to keep data safe.
-
Regularly Backing Up Data:
Regular backups of data help ensure that critical information can be recovered in the event of a data breach or loss. Backups should be stored in a secure location and encrypted to prevent unauthorized access.
-
Controlling Access to Data:
Controlling who has access to sensitive data helps to prevent unauthorized access and breaches. It is essential to implement access controls, such as authentication and authorization, to limit access to only those who need it.
Secure Networks
Another critical aspect of securing IoT devices is securing the networks they are connected to. IoT devices connect to networks, including local networks, the internet, and cloud services, to transmit and receive data. To secure these networks, it is essential to follow best practices, such as:
-
Securing Wireless Networks:
Wireless networks are vulnerable to attacks, including man-in-the-middle attacks, unauthorized access, and more. To secure wireless networks, it is essential to implement strong encryption, such as WPA2, and to regularly change the network’s password.
-
Monitoring Network Traffic:
Monitoring network traffic helps to identify and prevent potential security threats, including malware and unauthorized access attempts. Regularly monitoring network traffic and taking appropriate action in response to security threats helps to prevent breaches and protect sensitive information.
-
Implementing Network Segmentation:
Network segmentation helps to isolate critical systems and sensitive information from the rest of the network. This helps to prevent unauthorized access and reduce the impact of security breaches.
Secure IOT Devices
Finally, it is essential to secure the IoT devices themselves. From preventing unauthorized access to updating software, there are several best practices to follow to secure IoT devices, including:
-
Keeping Secure IOT Devices Up-to-Date:
Regularly updating software and firmware helps to keep IoT devices secure and protected against potential security threats. It is essential to keep devices up-to-date to ensure that they are protecting against the latest security threats.
-
Securing Physical Access:
Physical access to IoT devices should be restricted to prevent unauthorized access and tampering. Devices should be secured with locks or placed in secure locations to prevent theft or unauthorized access.
-
Monitoring Secure IOT Devices:
Monitoring IoT devices helps to identify potential security threats and take appropriate action. Regularly monitoring devices for unusual activity, such as unexpected network traffic or software changes, helps to prevent breaches and protect sensitive information.
Conclusion of Secure IoT Devices
Building secure IoT devices is crucial to ensure the protection of both data and devices. By implementing encryption, firewalls, and secure boot processes. As well as regularly updating software and conducting security audits, organizations can reduce the risk of security breaches and protect against potential threats. Additionally, using secure cloud platforms and deploying multi-factor authentication can provide an extra layer of security for IoT devices. By following these best practices, organizations can develop IoT devices that are secure and trustworthy, enabling the seamless integration of technology into daily life while protecting valuable data. The adoption of IoT technology has expected to continue its growth, making it more important than ever to prioritize security in the design and development process.
BACK